“In the middle of difficulty, there is opportunity.” -Albert Einstein
The COVID-19 pandemic has changed many aspects of life, and lately there has been a lot of discussion about the “old” normal and the “new” normal. One thing is for sure, employees at many companies will continue to work from home for one reason or another from here on out we are in the “new” normal.
As you review your remote work policy — not only for business continuity purposes but also as part of employee recruitment and retention — it’s important to consider all consequences of employees working remotely and learn more about fraud protection. While there are many benefits of remote work, it also means an ongoing risk of fraud to business in the form of monetary and data losses originating from cyberattacks, internal fraud, control weaknesses, and workflow inefficiencies. Once employees are working in a different environment, such as in a living room or at a kitchen counter, they may feel more comfortable and less professional, which can lead to an opportunity for cyber thieves. However, just like when they are in the office, employees should keep in mind fraud protection measures, remain vigilant, and suspiciously inspect emails and online business.
Business Fraud Risk #1: Cybersecurity Risks
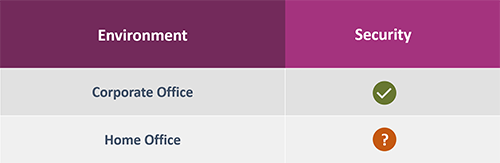 Employees with weak home network security should be an early focus of your efforts to mitigate risk of fraud in business or for your organization. As opposed to the office environment, where IT managers can effectively control the security of the company’s networks, employees’ home networks may use weaker protocols and default passwords, for example. This allows cyber thieves easier access to the network’s traffic.
Employees with weak home network security should be an early focus of your efforts to mitigate risk of fraud in business or for your organization. As opposed to the office environment, where IT managers can effectively control the security of the company’s networks, employees’ home networks may use weaker protocols and default passwords, for example. This allows cyber thieves easier access to the network’s traffic.
Take The Following Steps For Fraud Protection and To Help Prevent Cyber Attacks While Working Remote:
- Install properly configured and secured routers for workers at home.
- Implement multifactor authentication for your email system and other critical systems.
- Inspect every email received to ensure its legitimacy.
-
- Pay careful attention to the sender’s email address to ensure the accurate spelling of the complete address. Hover your mouse over the address to reveal the actual address.
- Beware if an email urges you to act quickly for any reason, especially if the action is out of the ordinary or instructs you to enter credentials anywhere.
-
- If you suspect an account is compromised, disconnect from all systems and change your password by following best practices for a strong and complex password.
- Train employees on best practices for accessing your company’s Virtual Private Network (VPN), hosting virtual meetings, etc.
- Don’t take shortcuts when following your established procedures.
- Continue following established programs for patch management, access control, and security monitoring.
Business Fraud Risk #2: Social Engineering Techniques Create Need For Fraud Protection
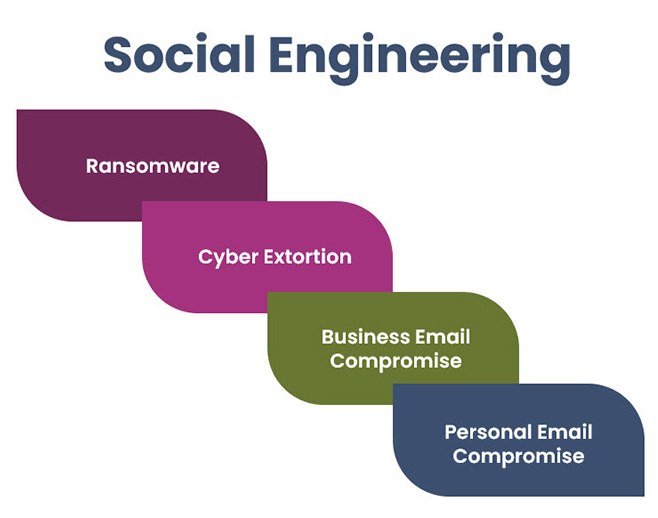 Successful social engineering techniques can lead to risk of fraud in business and malicious incidents such as ransomware, cyber extortion, business and personal email compromise, and the list goes on. These incidents are widely recognized as the top cause of data and monetary breaches. According to the 2019 Verizon Data Breach Report, business’s financial staff were the most likely to be compromised in incidents involving fraudulent transactions. It should be noted that executives were compromised in 20 percent of the incidents and are six times more likely to be the person compromised. Well-crafted phishing emails are the easiest and most successful method used by cyber thieves to gain access and control of company resources and online banking accounts and can lead to nefarious acts, such as instructing your employees to originate Automated Clearing House (ACH) or wire transfer transactions.
Successful social engineering techniques can lead to risk of fraud in business and malicious incidents such as ransomware, cyber extortion, business and personal email compromise, and the list goes on. These incidents are widely recognized as the top cause of data and monetary breaches. According to the 2019 Verizon Data Breach Report, business’s financial staff were the most likely to be compromised in incidents involving fraudulent transactions. It should be noted that executives were compromised in 20 percent of the incidents and are six times more likely to be the person compromised. Well-crafted phishing emails are the easiest and most successful method used by cyber thieves to gain access and control of company resources and online banking accounts and can lead to nefarious acts, such as instructing your employees to originate Automated Clearing House (ACH) or wire transfer transactions.
Take the following steps to help prevent against incidents from social engineering:
- Implement dual controls for all monetary transfer requests. Two employees should always be required to perform a monetary payment. This can be accomplished remotely via online banking.
- Perform out-of-band authentication for any changes to payment requests from third parties such as consultants and vendors. Calling the third party using an established phone number ensures the payment request is legitimate.
- Install and maintain anti-malware software on all endpoints, including devices at home.
- Implement email content filtering to reduce inbound phishing emails and spam.
- Train employees on best practices for dealing with suspected phishing emails.
- Develop and test an incident response plan.
Business Fraud Risk #3: Employee Theft And Physical Security
With unsupervised access to systems and information, employees working from home could more easily steal company or customer data and use it for personal gain. Breaches of customer data or proprietary secrets could lead to legal issues and lost funds at best; lost customers and reputation damage at worst. If your business works with sensitive data, such as in healthcare, be especially careful when allowing employees to work from home. Employees aren’t the only ones who could commit data theft. Roommates, family members, and visitors can pose a risk to the sensitive data. Physical security of company-issued devices is also a problem. This could be something as simple as leaving a device out in the open at home or in an unlocked car. Security breaches can happen simply because an unsecured device is stolen. Code42 reports that in airports alone, a laptop is taken every 53 seconds.
Take the following steps to help prevent against employee theft and physical security of devices:
- Limit employee access to systems and information to only those that they need access to perform their job functions.
- Implement a Data Leak Protection (DLP) solution and turn on system alerts for suspected sensitive data leaks.
- Block access to USB ports for all employees except an administrator.
- Issue company-owned devices to your employees and secure the devices with a device management solution. Enforce the activation of the “find my device” feature on all devices.
- Implement a company-wide screen timeout for 15 minutes of inactivity.
- Develop an Information System Acceptable Use Policy that clearly communicates to employees your expectations regarding their use of company resources.
There are inherent risks whenever company data flows through a home network. As the lines between home and work continue to blur, you must depend on your employees to exercise care by taking steps to secure their home networks and be mindful of fraud protection. Employees hold more of your company’s security in their hands than ever before, so the need for following security and fraud protection best practices and controls is vital.
Additional Resources
On May 1, 2020, the Department of Homeland Security Cybersecurity & Infrastructure Security Agency revised their telework guidance resource: CISA COVID-19 Telecom Resources Site.